In the IIoT era, data security is the lifeline. NEXSPC eliminates Public Cloud SaaS risks by insisting on 100% On-Premise deployment. Deploy on your factory intranet servers or private cloud, physically isolated (air-gapped) from external access to secure core process data. With advanced B/S (Browser/Server) architecture, access via any browser across the plant. Coupled with a one-time buyout (perpetual license) and unlimited users, NEXSPC saves you hundreds of thousands in long-term TCO.
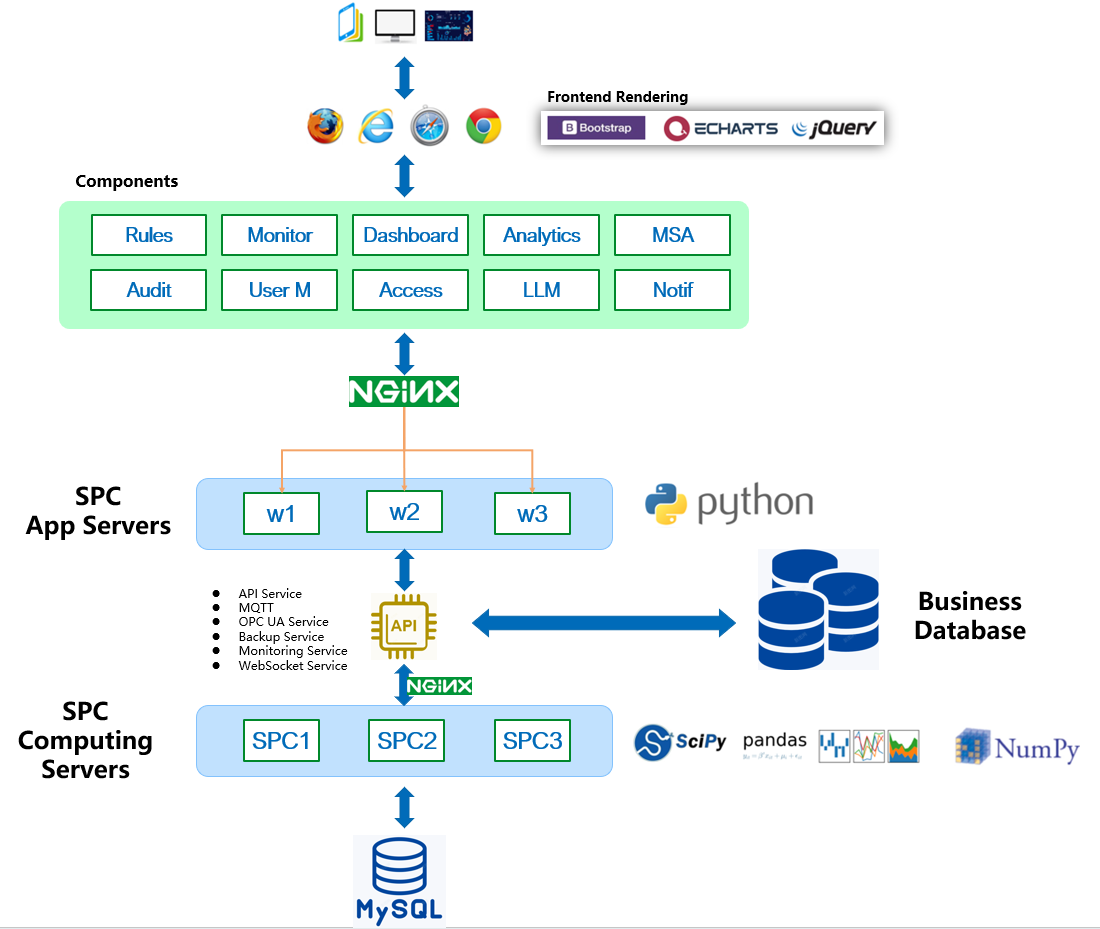
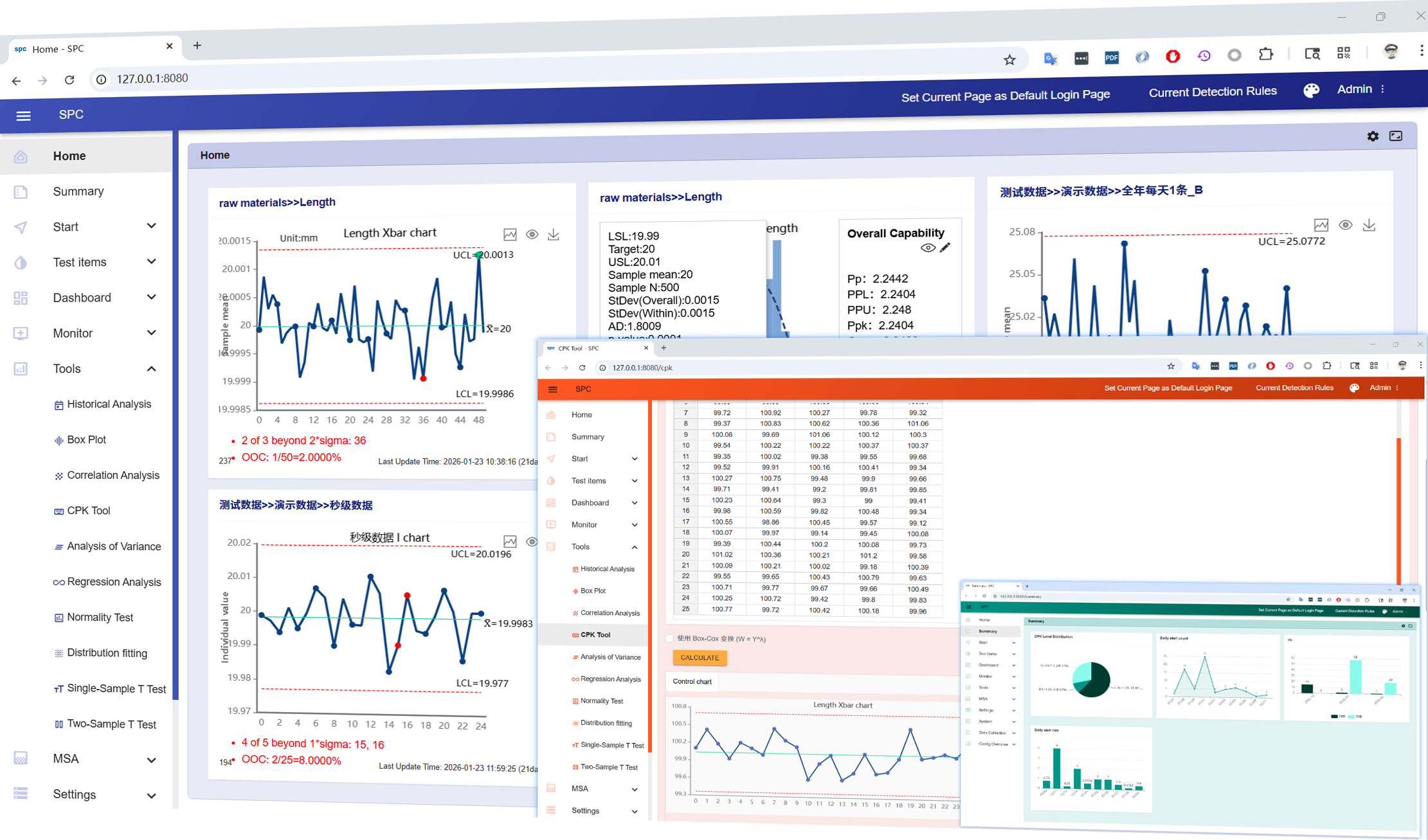
Pure B/S Architecture - Zero Installation, Full Coverage
NEXSPC uses modern Web technology. IT departments don't need to install software one-by-one on every terminal.
Perfectly compatible with Chrome, Edge, Firefox, and Safari. Access via URL on shop floor IPCs, office PCs, iPads, or Android tablets.
Upgrade once on the server, and all clients sync instantly. Say goodbye to the nightmare of version mismatches in traditional client software.
Runs smoothly on Windows, Linux, and macOS. Perfectly adapts to diverse office environments.

Data Sovereignty & Security
Inspection data is confidential manufacturing data.
System and database run entirely on your corporate intranet servers. Even if you unplug the internet cable, the system remains stable.
Supports database Master-Slave Hot Standby and scheduled automatic backup strategies.
Rigorous penetration testing ensures no backdoors and no hidden 3rd-party data telemetry. Peace of mind for IT and executives.
Lifetime License Model - Unlimited Users, Lifetime Purchase
Unlike the expensive 'Per User' or 'Annual Subscription' models of software like Minitab, NEXSPC promises:
No subscriptions. Pay once, use forever. Extremely high long-term ROI (Return on Investment).
Unlimited Users (Total Quality Management), Unlimited Inspection Points (Full Coverage), Unlimited Dashboards (Customization).
Scale your business without worrying about linear software cost growth. True 'Democratization of Quality Management'.
Globalization & Multi-language Support
For multinational manufacturers or factories with foreign employees, NEXSPC offers the industry's most comprehensive language pack support.
Built-in support for Simplified/Traditional Chinese, English, Japanese, Korean, Vietnamese, Thai, Indonesian, Spanish, and more.
Employees of different nationalities see their native language on the same system. For example, Chinese management views Chinese reports, while Vietnamese line workers use a Vietnamese input interface. Barrier-free cross-border collaboration.

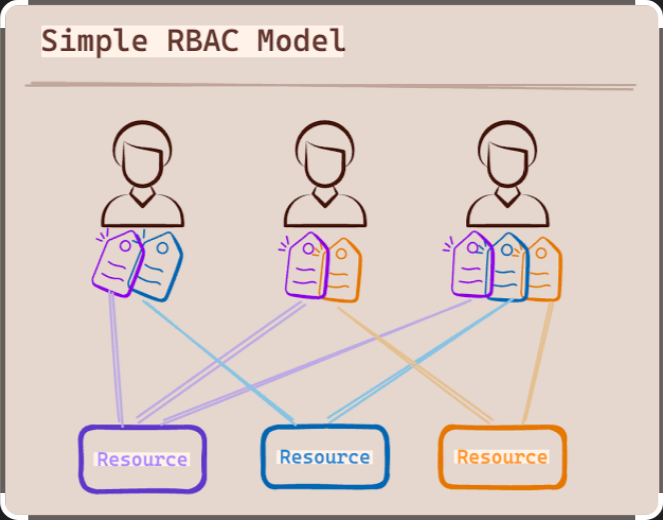
Fine-Grained Permission Control & RBAC
Security is not just about external threats, but internal ones too. Built-in powerful RBAC (Role-Based Access Control) model.
Permissions refined to 'Who can see which workshop', 'Who can modify specs', and 'Who can only input but not delete'.
Preset standard roles like Admin, Quality Engineer, Operator; supports custom roles.
Automatically records User, IP, and Time for all key actions (e.g., data modification, deletion). Ensures every change is traceable for compliance audits.